svenknebel.de / Indieweb
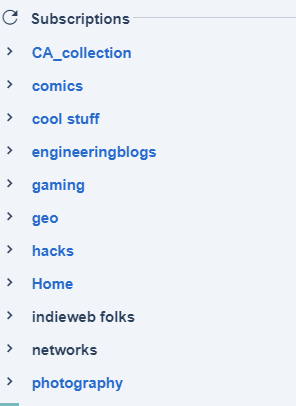
I've not only setup Inoreader to hide channels without unread content, I also removed the counts of unread posts (simply using my adblocker) to reduce the mental pressure. Maybe another option to consider?
Notes for HomebrewWebsiteClub 2017-04-05
Florian had brought a bunch of interesting links:
- ethicalweb.org
- fairwebservices.org
- ind.ie/ethical-design
- criticalengineering.org
- The Social Design of Technical Systems: Building technologies for communities
This led back to a discussion from 2 weeks before, where we had talked about about tracking and respecting user requests like the Do-Not-Track-header. Joel mentioned the CommonTerms project, which proposes icons for typical clauses in Terms and Conditions.
He showed how on one of his web pages, he does not just disable tracking for users that have the Do Not Track header set, it also clearly indicates this to users:
“Active tracking using Piwik on this page has been disabled based on your browser's Do Not Track (DNT) setting.”
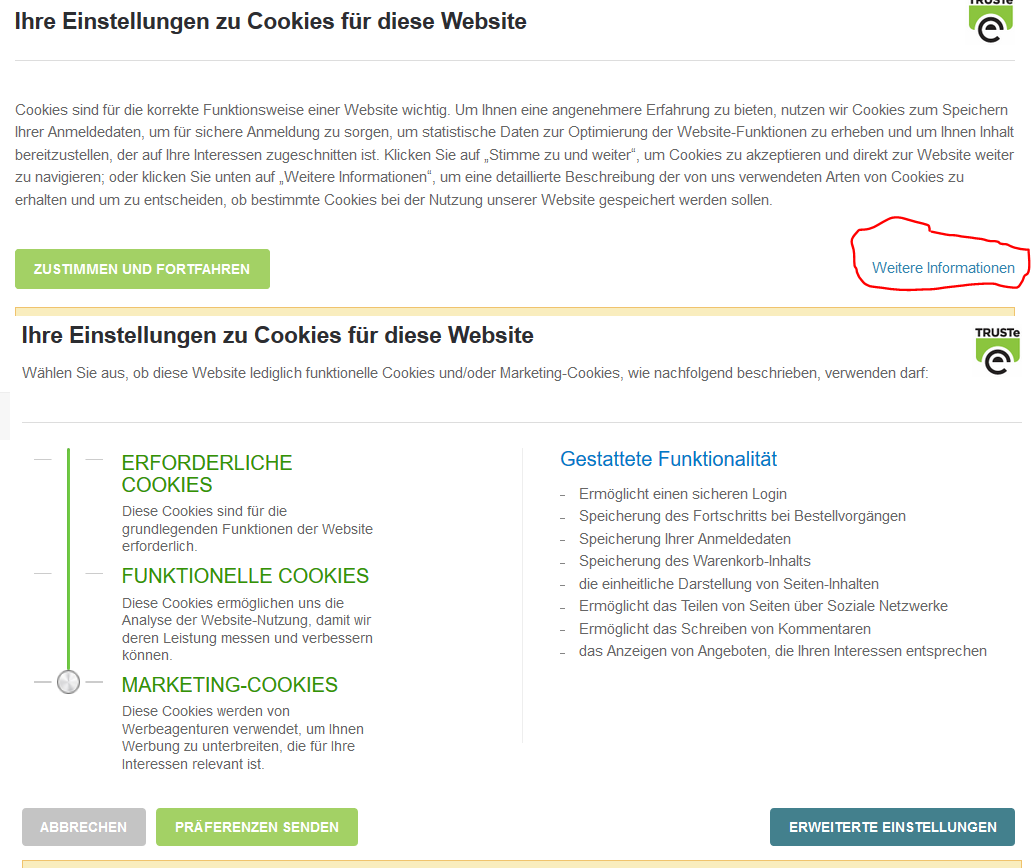
Another example are the cookie banners made by TRUSTe, which allow a visitor to choose between different types of cookies used, if they find the right link to click:
Differential privacy was mentioned, but nobody knew enough to really talk about it. Here is a slide deck about the topic a friend made a few years ago.
Another privacy aspect covered was how federated/distributed systems by design create many additional copies of data, with less centralized control over them. This is of course a desired property, but it also means that these copies might be hard to delete and are presented in different aggregations users might not be aware of. While a deleted silo post is expected to be gone from outside of dedicated archives, a deleted post on a GNU Social/Mastodon instance likely is still visible on other federated instances. If one instance blocks search engines using robots.txt, content from it still might be indexed on other sites. In an IndieWeb context, a site that backfeeds from Twitter likely still shows deleted interactions (and in general shows them in an unexpected context). Many IndieWeb tools also have public logs or APIs retaining data, which might be surprising to users. (e.g. brid.gy, webmention.io)
Other random links that were mentioned:
- Meddelare by Joel, for showing aggregate counts of silo interactions, proxied through a private server.
- some notes on privacy settings for Wordpress installations
Talking about our private sites, only I had progress to present: I improved my Micropub endpoint, and I have now explicit headers for replies, bookmarks, …: example post
notes for HWC Berlin 2017-03-08
At we talked a bit about the recently released W3C Annotation standards and annotations in general. The W3C standards have many ways of addressing content (“selectors”), many of which likely only work against a specific version of a document and site design. But there is a way to specify timestamps and link archived copies.
Examples of annotation UIs (not using the W3C standards (yet)): related Indieweb components:- Fragmentions as a very simple way of linking to specific text locations in URL fragments. A more complex variation of this is described in the W3C annotation standard as well.
- The W3C standards do not specify how to notify sites of (public) annotations created elsewhere, despite showing this in the explanatory diagrams. Webmentions would be a natural fit for this: A receiver that implements the JSON-verification suggested in the standard already would at least recognize a stored annotation as a valid source, and could be extended to understand the entire representation and display it nicely.
Some discussion about (over-)sharing in social media, your own website, and a trend to move social media content to private channels.
Joel found the Indieweb wiki because he found Indieauth.com while searching for a new OpenID provider, and joined us.
References from last time:- aaronpk has built an IRC-based chat widget for his homepage, inspired by our discussion
- Sebastian now uses his Wordpress login for Indieauth
- I (Sven) am working on a 2FA indieauth endpoint
- JSON Web Tokens as a standard way to create signed tokens with payloads, useful for e.g. authentication endpoints.
Some notes for HWC Berlin 2017-02-22
- We talked about various messaging-related topics:
- Matrix.org as a relatively new and open messaging protocol.
- The private webmention specification created from IWC Brighton.
- Sebastian would like a chat interface on his contact page so visitors can quickly talk to him if he is available. There are bunch of services targeted at e-commerce sites, but from a quick review not much suitable for individual pages. This was also discussed on IRC. (I’ll probably follow up on this in another post, once I ordered my ideas a bit)
- IndieAuth-the-protocol – several attendees weren't aware that they can use their own systems (e.g. existing website login) for IndieAuth and want to implement this now. Documentation for the necessary authorization endpoint is here.
- Security: Caddy server has a new fingerprinting feature to detect TLS interception proxies. One could show a warning to users along the lines of “Your HTTPS looks wonky. <yeah, I know> <HELP>”. I tried to think of additional ways to detect this, but the only one I could come up with, detecting missing HPKP headers using Javascript, wouldn't work because Firefox and Chrome ignore HPKP on local trust roots, so there is no need for a proxy to strip those.